Top 15 Best Devise Alternatives In 2022

Devise is a scalable authentication solution for Rails that can be used to secure both online applications and API services. It accepts username/password credentials, account authentication using Facebook, Twitter, GitHub, etc., and token-based authentication. Additionally, it has tools for managing authentication sessions, integrating social login, and recording user activities. The tool provides with a variety of adapters that will get you up and running quickly, but it is also simple to develop your own adapter if necessary. It is meant to be highly extendable to work with any Rack-based web application.
Admin, User, and Guest are just a few of the built-in authority, but you may also quickly create your own if necessary. The encoder ActiveRecord:: User data is encoded and decoded using Base and JSON. Additionally, there is support for a number of authentication rules, such as remember me, passwordless, and two-factor authentication.
Top 15 Best Devise Alternatives In 2022
In this article, you can know about devise alternatives here are the details below;
1. Passport

For Node.js-based apps, Passport serves as an authentication solution. Several methods, such as cookies, tokens, and user pools, can be used to authenticate users. It’s modular architecture makes it simple to integrate into any online application. It may be used to build secure apps as well as approve requests. Passport may be utilised in any Express-based application, is easy to use, and requires little configuration. This is another Devise alternative.
Session, cookie, and token-based authentication are just a few of the authentication methods included in Passport. The application supports third-party login services like Facebook and Twitter as well as business identity providers, social networks, and other methods of authentication. It also supports a wide scope of authentication methods.
2. Spring Security’s

This is another Devise alternative. Modern online applications may benefit from Spring Security’s top-notch authentication and access-control framework, which offers a complete security solution that addresses authentication, authorization, and security-related messaging. Additionally, it has functions like social login, form-based authentication, and message encryption. The application was made available as open source and under the Apache 2.0 licence. It offers a complete security solution for Java applications by building on top of the Java Security Architecture. The framework’s high degree of adaptability makes it simple to fit it to the particular requirements of your application.
You can easily combine Spring Security with your current infrastructure and fine-tune security settings to suit your unique needs. Basic authentication, form-based authentication, and Oauth2 are just a few of the many authentication methods that Spring Security offers. Its robust access control list system lets you limit what users may accomplish. It can also serve as a security token service, enabling the safe transfer of tokens across different systems.
3. JSON Web Token

A standard URL-safe tool called JSON Web Token (JWT) enables you to send information between parties as a JSON object. It makes it possible to independently verify assertions without the involvement of the people making them. A JSON object serving as the data structure includes three specified fields. The terms “header” and “payload” each include meta-data about the token, the terms “signature” and “payload” both contain the payload’s digital signature made with JSON Web Signature. This can assist to guarantee that only permitted users have access to information or resources. It may be applied to server-side programmes as well as browsers.
JWT is ideal for AJAX applications since it works with any transport protocol, including HTTP. Furthermore, JWT may be encrypted in a number of ways, making it impossible for someone to read the contents of the token even if they manage to intercept it. JWT is tamper-proof, making it challenging to change the contents of the token covertly. This contributes to the security of the data transmission. This is another Devise alternative.
4. Django REST framework JWT

REST framework for Django For your Django REST API, JWT is a JSON-based Web application authentication solution that offers quick, safe authentication. It transmits data between the client and server using the JSON Web Token standard and has built-in security measures to protect your data. The definition of the authentication schemes is always expressed as a class list.
Every class in the list will be tried for authentication by the REST framework, and it will only return the value of the first class that succeeds. Create a JSON object containing the needed data and sign it with a secret key to utilise the tool. The recipient can check the signature and decode the data after receiving it.
5. LDAP

In a networked context, LDAP may be used to store and retrieve data about users, groups, and devices as well as to offer authentication and authorization services. Some of the key characteristics are standardisation, which is based on industry-standard protocols and makes it interoperable with a wide range of software, flexibility, which helps the tool adapt to meet a variety of needs, and ease of use, which results in a simple syntax and can be accessed using a variety of tools. Also check disk imaging software
This is another Devise alternative. Multiple servers may be used to disseminate an LDAP directory. Each server may have a duplicated copy of the whole directory that is regularly synced. When a server accepts a request from a user, it assumes responsibility for it, passing it on to other DSAs if required while making sure the user receives a single coordinated answer.
6. OmniAuth

OmniAuth is a Ruby authentication framework for websites that offers a common interface for integrating with many authentication providers, including Facebook, Twitter, GitHub, Tumblr, and more. Developers no longer need to build bespoke code to provide authentication to their web apps thanks to this. It may be used with any Ruby web framework as it is meant to be rack-compatible. As a result, developers are free to concentrate on the functionality of their programme because the authentication process is abstracted away.
A variety of other capabilities, including as cross-site request forgery defence and built-in support for session management, are also provided by OmniAuth to facilitate authentication. It also comes with adapters for well-known Ruby frameworks like Sinatra and Ruby on Rails. You can only add the providers you require because the tool is modular in design. Overall, OmniAuth is a fantastic product that you may take into account as one of its substitutes.
7. Firebase Authentication

A scalable token-based authorization solution for your apps, Firebase Authentication offers client SDKs and backend services for authentication with various identity providers. With the use of this machine, you can quickly create a secure authentication system for your app. The tool is readily integrated with other Firebase capabilities, such as its Realtime Database and Cloud Messaging, because to its extensibility. You can make and manage user accounts, authenticate users using their email address and password, and do a lot more using Firebase Authentication. This is another Devise alternative.
In addition to Sign-In and email/password authentication, it also supports social identity providers like Facebook and Twitter. Additionally, you may design your own unique authentication provider. It offers libraries for well-known programming languages including Java, Objective-C, and Swift in addition to SDKs. Overall, Firebase Authentication is a fantastic technology that you may take into account as one of its substitutes.
8. OAuth2
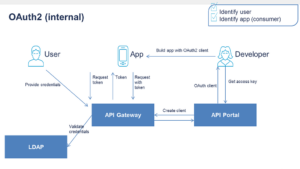
Oauth2 is a framework for web application authorisation that enables safe data access without the requirement for user credentials to be stored. Additionally, it enables programmes to confirm users’ identities without requesting their passwords. The tool does not just use these authorization flows or techniques; it also defines other ones. Many well-known online systems now employ Oauth2 as the industry standard for authorisation. Applications can utilise it to safely access data that is kept on a user’s device or on a distant server.
Oauth2 also enables programmes to exchange data without needing users to divulge their login information. Oauth2 is based on the Oauth 1.0 standard, however it has undergone considerable revisions to fix security flaws and improve usability. The main distinction between Oauth1.0a and Oauth2 is that Oauth2 authorises access to resources using bearer tokens rather than cookies or session IDs.
9. OAuth.io

This is another Devise alternative. With only a rare lines of code, developers can easily add authentication or social logins to their online apps using Oauth.io, a supplier of web app integration and authentication. It provides libraries for all the major programming languages and supports all the major providers. Additionally, you may have a strong API that enables you to integrate authentication to your own unique apps.
Oauth.io has a simple setup process, comprehensive documentation, and an appealing user interface. With a variety of authentication techniques, including passwordless, two-factor authentication, etc., it allows social login, single sign-on, and business login.
10. Sso

Sso is a user and session login authentication service that offers your users a quick and safe method to sign in to your online apps. While offering a fantastic user experience, you can effortlessly manage user sessions, access control, and keep your user data safe. It enables single sign-on and federated sign-in and offers a centralised approach to manage the authentication procedure for online applications and services. Users may be authenticated using Fso against a variety of identity sources, including Active Directory, LDAP, and others.
Additionally, Sso protects your data using secure protocols like HTTPS and TLS. It’s perfect for businesses that need to control user access to a variety of web services. By using the check session method, which will try to discreetly authenticate the user within an iframe, you may verify a user’s Sso status from an application.
11. OneLogin

OneLogin is a market-leading Identity and Access Management tool created specifically to make company logins easier while enhancing system security and effectiveness. The system is utilized by thousands of companies and people because it is quick and simple to set up and helps streamline many user workflows and procedures, increasing productivity without compromising security. Also check MRI Software
All users, apps, and other devices are brought together in a tightly integrated cloud-based system with the aid of OneLogin. It facilitates IAM (Identity and Access Management), making it quick and simple for users to apply your policy as intended, while lightening the strain on your IT department and allowing it to focus on its identity first approach. This is another Devise alternative.
Your staff has access to the applications that have been verified to comply with policy thanks to the system. Due to the solution’s enterprise agility and secure application access, any device in your company is protected. The whole network and company, including corporate workstations, web apps, and mobile devices, are subject to this protection in full. OneLogin is a straightforward yet effective programme that controls your whole system. Additionally, it possesses a number of noteworthy characteristics that add to its allure.
12. AuthAnvil

Another programme specifically created to assist IT teams in maintaining the security of their networks, infrastructure, and devices at all times—including outside of business hours—is AuthAnvil. One of the top platforms, it offers a variety of cutting-edge features that set it apart from rivals.
The solution relieves your IT staff of the responsibility of password management so they can spend more time making sure your networks are all operational and your data is completely safe. The application’s biggest feature is its ability to integrate password management, single sign-on, and multi-factor authentication capabilities, which effectively eliminates password bugs that both users and IT administrators encounter.
Users may easily access their accounts, data, and systems with the use of this programme without having to remember their passwords.
13. TeamPassword

This is another Devise alternative. For software design and development teams, advertising agencies, and creative companies, TeamPassword is an all-in-one cloud-based password management system. It is a little different from it from Okta and has many more cutting-edge features, which makes it superior to others. The solution offers effective methods for managing numerous logins and passwords.
Additionally, it makes it possible for organisations, teams, and companies of all sizes to quickly manage and distribute passwords for the software, services, and tools needed to complete tasks. Users of TeamPassword may establish team passwords, choose the level of access to each password, get notifications, and do other things. It is a rather straightforward tool that enables users to control, add, and distribute passwords for internal clients.
Companies are able to contact with one another to discuss their initiatives thanks to this service. One of the application’s most compelling features is its secure built-in password generator, which enables you to generate an infinite number of strong passwords.
14. WebTitan

A platform for malware prevention and web content filtering called WebTitan is designed specifically for managed service providers, retailers, public buildings, and WiFi hotspot providers. Businesses and organisations can secure their employees and consumers when they are online thanks to this simple and one of the finest deployment options that may be either on-premises or in the cloud.
It gives users the power to block access to objectionable and improper content, such as pornography, hate speech, and any other types of forbidden material. WebTitan makes it possible to restrict the information that clients and visitors may access, guaranteeing that they are safe from all types of online dangers including malware and phishing. Also check data recovery apps
The platform has thorough reporting capabilities that help businesses create rules to provide a secure environment for their users and workers. Similar to previous apps, it provides a number of noteworthy features, including automatic scheduling, behavior-based reporting, different filters, a live display of user browsing activities, and PDF and Excel export options.
15. Teramind

Another employee monitoring tool and computer security platform is Teramind, which keeps tabs on what workers are doing online while also defending the network against possible dangers like information theft, etc. It is one of the greatest Okta alternatives that provides all the same services while adding a few special features that set it separated from the competition.
This technology allows all businesses to identify potentially dangerous security risks, isolate suspicious activities, and track staff productivity and efficiency. By providing them with real-time notifications, the service also helps IT security and owners reduce security incidents. Teramind also locks users, and gadgets appear to be a danger to the organization’s credibility. This is another Devise alternative.
The ability to play back employee activity history allows businesses to interactively examine their employees’ activity at the back of the day or at any moment, which is one of the application’s most interesting and pleasant features. The platform also has capabilities like email monitoring, keyloggers, file tracking, automatic behaviour rules, and project management integration.



